ZK Proofs Protecting Newbie Crypto Wallets from Hacks and Drains 2026

In 2026, as cryptocurrency adoption surges among everyday users, crypto newbie wallet security remains a glaring vulnerability. Newcomers, eager to dive into DeFi or hold their first Bitcoin, often fall prey to phishing scams, malware, and sophisticated drains that siphon funds in seconds. Traditional wallets expose private keys or transaction details on public blockchains, turning user error into catastrophic loss. Enter zero knowledge beginner wallets powered by ZK proofs: a cryptographic shield that verifies actions without leaking secrets. This technology isn’t just theoretical; it’s actively fortifying wallets against the hacks that plague novices.

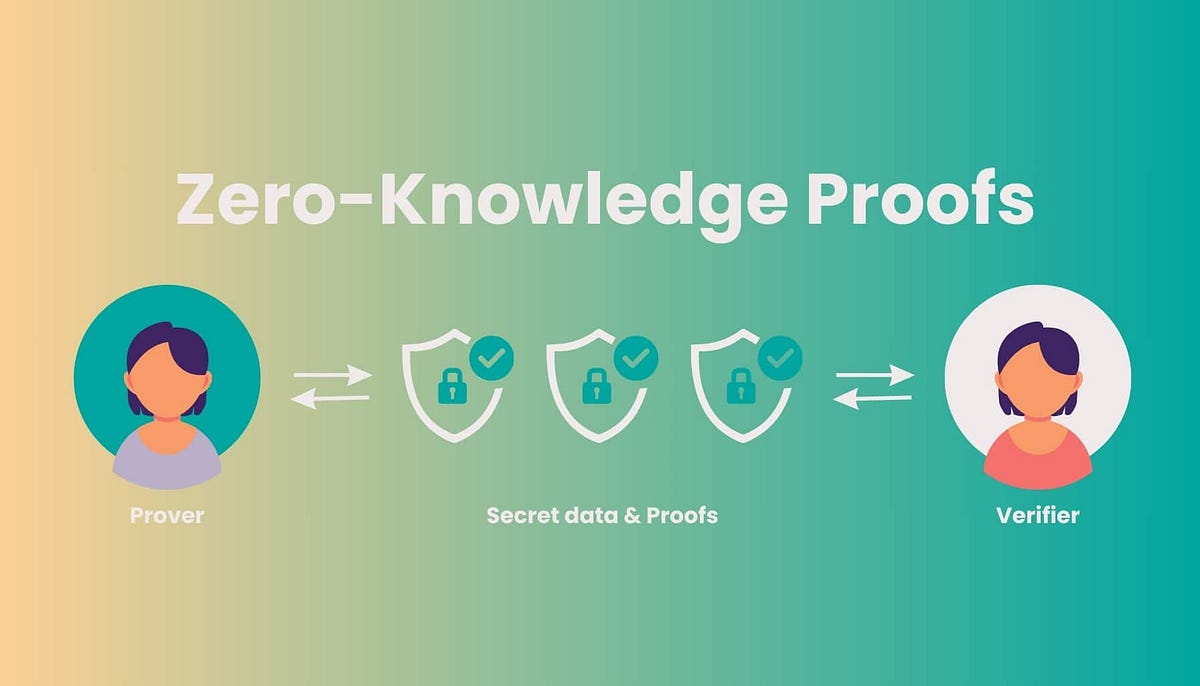
Consider the anatomy of a typical wallet hack. A beginner clicks a malicious link, signs a transaction unknowingly approving unlimited spending, or falls for a fake app update. Blockchains like Ethereum broadcast every detail publicly, allowing attackers to monitor balances and patterns. ZK proofs wallet protection flips this script by enabling proofs of validity without disclosure. You prove ‘I have sufficient balance and authorize this spend’ without revealing amounts or addresses. It’s like showing a locked box contains gold without opening it.
Why Newbies Need ZK Privacy More Than Ever
Seasoned traders spot red flags, but beginners broadcast their inexperience through on-chain footprints: small test transactions, clustered holdings, or panicked sells. Attackers scrape this data to target the unwary. In 2026, with mobile wallets dominating, resource constraints amplify risks; lightweight apps struggle with full node verification. ZKPs solve this elegantly. Protocols compress massive computations into tiny proofs verifiable in milliseconds on any device. No more trusting centralized APIs that log your every move.
Take zk-SNARKs, the workhorse of modern privacy. They mathematically enforce ‘soundness’ – you can’t fake a proof – and ‘zero-knowledge’ – no extra info leaks. For zk privacy for new crypto users, this means shielding DeFi interactions. Imagine swapping tokens on Uniswap without revealing your portfolio size or strategy. Attackers see a black box, not a treasure map.
Unpacking ZKPs: From Theory to Wallet Reality
At its core, a zero-knowledge proof involves three properties: completeness (honest prover convinces verifier), soundness (cheaters fail), and zero-knowledge (verifier learns nothing beyond truth). In practice, for wallets, this manifests in layered defenses. A user generates a proof off-chain, submits it on-chain for validation. Ethereum’s layer-2s like zkSync natively support this, slashing gas fees while boosting privacy.
Real-world example: Unwallet’s privacy pools mix funds anonymously before ZK verification ensures no double-spends. Stealth addresses, one-time recipients derived from public keys, pair perfectly with proofs. Sender knows the view key to reclaim unspent funds; outsiders see noise. This combo thwarts chain analysis firms selling hack intel to criminals.
5 Ways ZK Proofs Stop Wallet Hacks
-
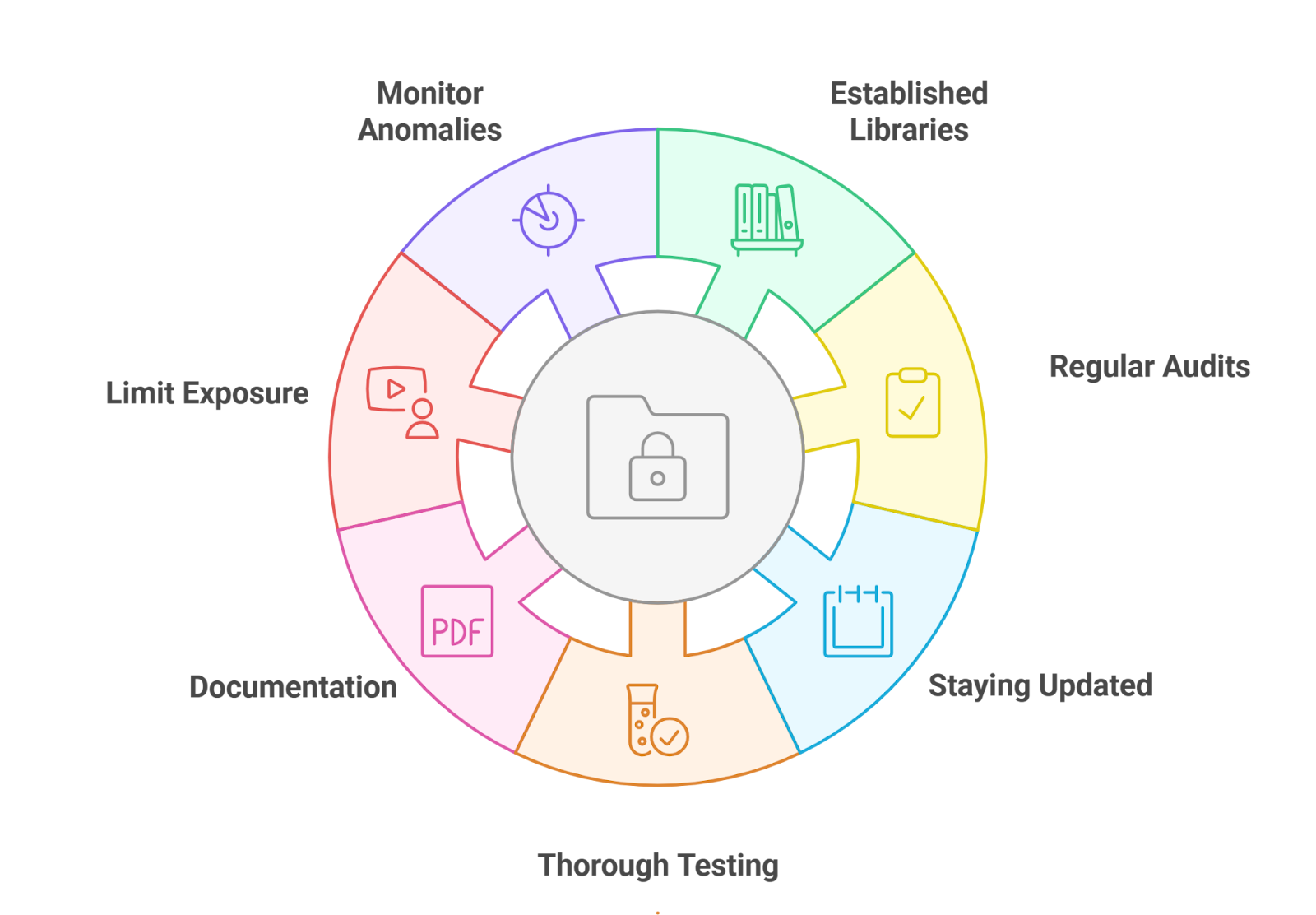
Hide balances to avoid targeting: ZKPs conceal transaction amounts and balances, as in Zcash shielded transactions or Unwallet‘s privacy pools and stealth addresses.
-

Prove approvals without key exposure: Users verify ownership or approvals via ZKPs without revealing private keys or credentials, reducing phishing risks.
-

Verify software integrity sans vuln details: Tools like CHEESECLOTH prove vulnerabilities exist for patching without disclosing exploit details (paper).
-
Enable compliant KYC without doxxing: Prove regulatory compliance (e.g., AML) via ZKPs without revealing personal data (source).
-

Compress proofs for mobile efficiency: Succinct zk-SNARKs in wallets like FeatherWallet enable fast verification on low-resource devices (paper).
Secure Authentication: Proving Identity Without Giving It Away
Passwordless auth is the holy grail for prevent wallet hacks with zk. Legacy wallets demand seed phrases memorized or stored insecurely. ZKPs enable ‘prove you control this key’ without signing arbitrary messages phishing bait. Soulbound tokens or decentralized IDs use ZK to attest attributes – ‘I’m over 18’ or ‘KYC verified’ – sans personal data.
FeatherWallet exemplifies mobile-first design: zk-SNARKs validate blockchain state with minimal battery drain. Newbies tap ‘send, ‘ the app crafts a proof, and boom – secure tx without full sync. Developers prioritize UX; no more ‘gas estimation failed’ terror. Yet, opinion: we’re not there yet. Proving latency must drop below 100ms for mass adoption, and hardware enclaves could accelerate this.
Software integrity checks via ZK take it further. Wallets prove ‘my code matches audited version’ without source reveal. Vulnerabilities stay secret until patched, starving zero-days. CHEESECLOTH-like tools let auditors collaborate blindly. For novices, this means downloading updates confidently, no second-guessing APK hashes.
Layer-2 ecosystems amplify these gains. zkSync and Polygon zkEVM bundle transactions into proof batches, slashing costs for small sends that newbies favor. A $10 coffee run in crypto stays private and cheap, no frontrunning bots sniffing patterns. Opinion: this scalability edge positions ZK wallets as the default for mass onboarding, outpacing clunky multisig setups.
Regulatory Balance: Privacy Without Blind Spots
Governments demand transparency amid crypto’s growth, yet zk privacy for new crypto users navigates this tightrope via selective disclosure. Prove ‘funds are compliant’ – sourced legally, no taint from hacks – without baring full histories. Neuronovai’s frameworks let wallets attest KYC status or AML checks cryptographically. Newbies comply effortlessly; regulators verify without invasive scans. This isn’t compromise; it’s evolution. Traditional audits expose everything, inviting doxxing. ZKPs filter truth surgically.
Challenges persist, though. Prover centralization risks ‘honest but curious’ operators peeking at inputs. Decentralized provers, like those in Succinct’s stack, distribute load across nodes, mimicking blockchain consensus. For novices, this means trust-minimized apps where security scales with network participation. We’re charting bullish patterns here: ZK token volumes spike on prover network launches, signaling adoption breakouts.
zkSync Technical Analysis Chart
Analysis by Sophia Patel | Symbol: BINANCE:ZKUSDT | Interval: 1h | Drawings: 7
Technical Analysis Summary
As Sophia Patel, my drawing instructions for this ZKUSDT chart emphasize precision in capturing L2 sequencer-driven volatility patterns. Start with a bold red downtrend line connecting the Mar 8 peak at 0.185 to the Mar 29 trough at 0.092, highlighting the dominant bearish channel amid high transaction latency spikes visible in candle shadows. Overlay horizontal lines at key support 0.090 (strong, recent lows tested thrice) and resistance 0.110 (moderate, failed retests). Mark a consolidation rectangle from Mar 20 (0.105 high) to Mar 26 (0.115 low) using date_price_range tool. Add fib retracement from Mar 8 high to Mar 29 low, focusing on 38.2% at 0.125 for potential bounce. Place arrow_mark_down at Mar 29 close for MACD bearish crossover confirmation, and callout on volume for ‘declining volume on downside suggesting exhaustion’. Every sequencer metric paints a chart story—these lines reveal reorg frequency easing into support.
Risk Assessment: medium
Analysis: Bearish trend dominant but exhaustion signals and strong support suggest balanced risk; L2 volatility per my SharedSeqWatch data tempers downside
Sophia Patel’s Recommendation: Hold for support bounce confirmation, enter long at 0.092 with tight stops—ZK privacy tailwinds loom if latency eases
Key Support & Resistance Levels
📈 Support Levels:
-
$0.09 – Strong multi-test low, aligns with fib 0% extension
strong -
$0.085 – Psychological round number below recent lows
weak
📉 Resistance Levels:
-
$0.11 – Moderate resistance from Mar 23-26 highs, failed breaks
moderate -
$0.125 – Fib 38.2% retracement, prior swing high
moderate
Trading Zones (medium risk tolerance)
🎯 Entry Zones:
-
$0.092 – Bounce from strong support with volume exhaustion, sequencer latency peaking—medium risk long setup
medium risk
🚪 Exit Zones:
-
$0.11 – First resistance target, channel midline
💰 profit target -
$0.085 – Invalidation below psych support
🛡️ stop loss
Technical Indicators Analysis
📊 Volume Analysis:
Pattern: declining on downside
Volume spikes on initial drop Mar 8-14, now contracting suggesting seller exhaustion—bullish divergence potential
📈 MACD Analysis:
Signal: bearish crossover
MACD line below signal with histogram contracting, but watch for divergence near lows
Applied TradingView Drawing Utilities
This chart analysis utilizes the following professional drawing tools:
Disclaimer: This technical analysis by Sophia Patel is for educational purposes only and should not be considered as financial advice.
Trading involves risk, and you should always do your own research before making investment decisions.
Past performance does not guarantee future results. The analysis reflects the author’s personal methodology and risk tolerance (medium).
Real-user wins emerge in 2026’s ecosystem. Unwallet’s dual privacy pools and stealth addresses exemplify zk proofs wallet protection. Funds tumble anonymously; ZK confirms ownership sans links to origins. Pair with hardware wallets like Ledger’s ZK modules, and you’ve got ironclad defense. Beginners activate with one tap, no seed phrase rituals prone to social engineering.
Hands-On Defenses: ZK Tools Every Newbie Should Use
FeatherWallet leads mobile charge, zk-SNARKs crunching proofs on-device for featherweight syncs. No data leaves your phone; full verification in seconds. Developers embed gasless simulations: preview tx impacts privately before broadcast. This preempts ‘infinite approval’ disasters, where users greenlight drains unwittingly.
Broader toolkit: privacy pools for mixing, oracle proofs for off-chain price feeds without manipulation vectors, and covenant scripts enforcing spend rules post-proof. Imagine wallets auto-rejecting suspicious patterns, like rapid micro-transfers signaling malware. ZKPs make this deterministic, not heuristic guesswork.
Yet, adoption hinges on education. Newbies grasp concepts via analogies: ZK is your wallet’s invisibility cloak in a panopticon chain. Charts confirm momentum; ZK protocol TVL mirrors 2021 DeFi boom, but with privacy moats fending off exploits. As a chartist, I see resistance breaks at key levels, forecasting ZK wallets capturing 40% newbie market share by year-end.
Forward gaze: FHE hybrids supercharge this, computing over encrypted balances on-chain. No proofs needed for simple ops; full homomorphic magic. Combined, they forge crypto newbie wallet security impervious to quantum threats looming. Developers, prioritize: ship intuitive ZK-first wallets, and watch hacks plummet. Users, demand them. In privacy’s arena, charts don’t lie – ZK dominance is scripted.








