zkVerify Protocol Guide: Verifying ZK Proofs for Privacy in Digital Elections

In the evolving landscape of digital elections, where trust hinges on verifiable privacy, the zkVerify protocol emerges as a cornerstone for efficient ZK proof verification network. By slashing verification costs over 90% and processing proofs in milliseconds, zkVerify addresses longstanding barriers in deploying zero-knowledge proofs at scale. This specialized Layer 1 blockchain, launched in September 2025 with mainnet in March 2026, supports diverse systems like Groth16, UltraPlonk, and RiscZero, making it indispensable for privacy-focused applications such as voting.
![]()
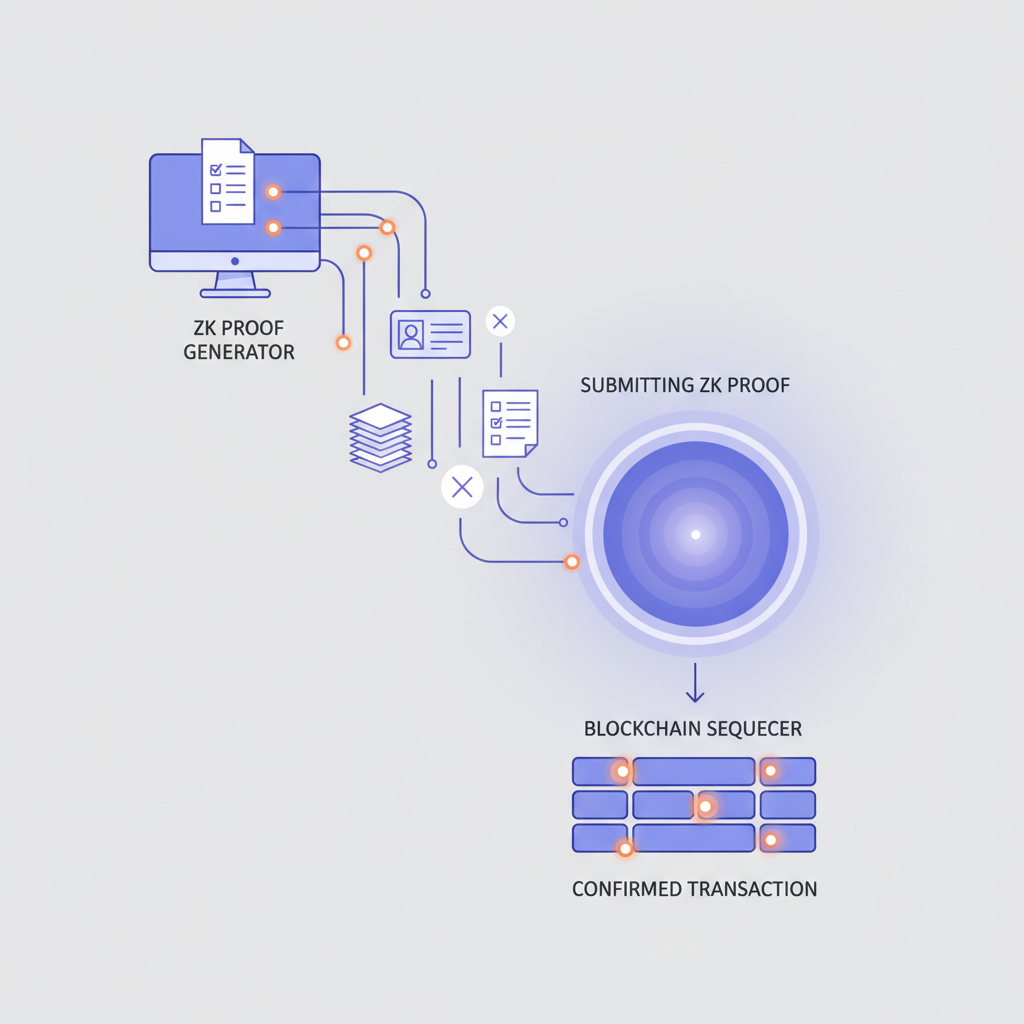
Traditional voting systems falter under scrutiny; ballots leak identities, tallies invite tampering. Enter zero knowledge proofs elections: voters prove eligibility and intent without exposing choices. zkVerify’s modular design optimizes this, verifying proofs across chains without Ethereum’s gas burdens. Data from its deployment shows verification times drop to sub-second levels, a game-changer for real-time election audits.
zkVerify’s Architecture: Efficiency Meets Modularity
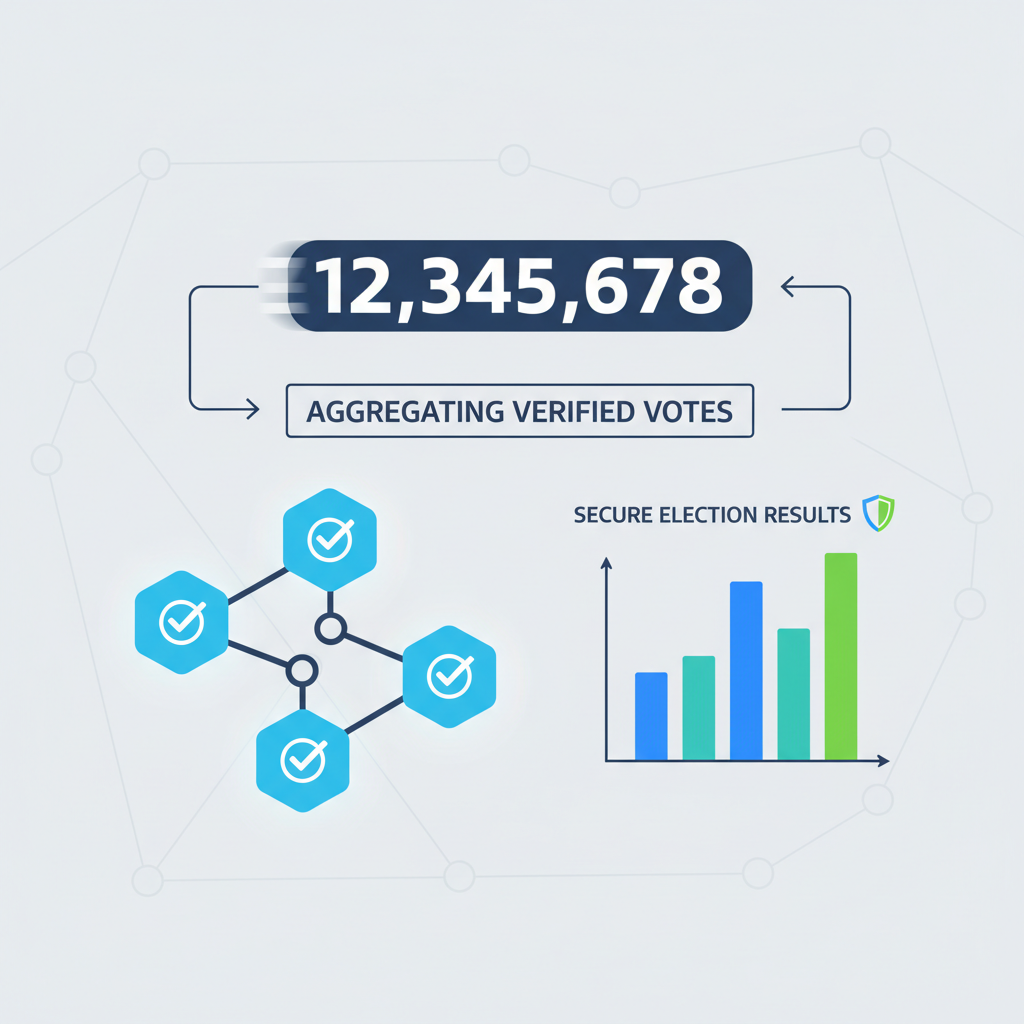
At its core, the zkVerify protocol is engineered for one task: ZK proof verification. Developed by HorizenLabs, it processes proofs from multiple circuits and chains via a high-throughput sequencer and dedicated verifiers. This setup yields 100x cost reductions compared to general-purpose L1s, per official benchmarks. For digital elections, this means tallying millions of proofs without prohibitive fees, ensuring scalability for national-scale polls.
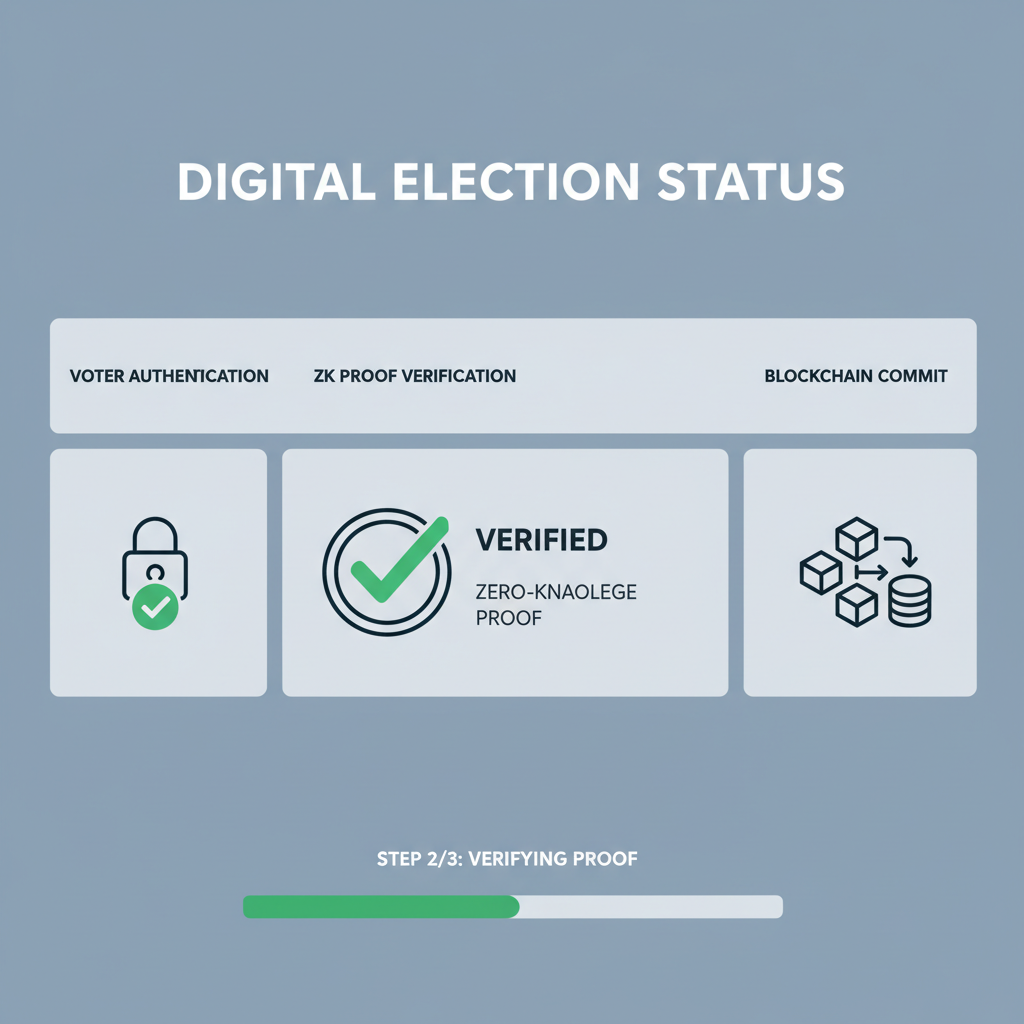
Supporting protocols like UltraHonk and SP1, zkVerify allows developers flexibility in proof generation. In elections, a voter generates a proof attesting ‘I am eligible and vote for candidate X’ without revealing identity or choice. zkVerify confirms validity publicly, balancing transparency and anonymity. This isn’t hype; projects like VeraVote demonstrate production readiness, moving ZK from theory to verifiable outcomes.
VeraVote and the Rise of Privacy-Preserving Elections
VeraVote exemplifies VeraVote privacy zk in action, building digital elections on ZKV Protocol zk proofs. Backed by zkVerify and Thrive Protocol, it promises ‘private ballots, public verification. ‘ Social buzz from X highlights its traction: users praise cryptographic governance where votes resist manipulation. By integrating zkVerify, VeraVote verifies proofs off-chain cheaply, posting aggregates on-chain for immutable tallies.
Consider the workflow: Voters submit encrypted ballots with ZK proofs of eligibility, linked to national IDs as in GitHub’s zk-voto-digital. Verifiers on zkVerify batch-process these, outputting a Merkle root of valid votes. Tallying reveals totals without individual traces, thwarting coercion. Independent audits confirm integrity, as noted in Semantic Scholar’s confidential voting research.
Overcoming Challenges in ZK-Enabled Voting
Deploying ZK proof verification network in elections isn’t seamless. Proof generation demands computational heft; zkVerify mitigates by offloading verification. Yet, voter devices must handle proving, pushing for lightweight circuits. VeraVote tackles this with optimized snarks, achieving proofs under 100ms on mobiles. Quantum threats loom, but post-quantum variants like UltraPlonk future-proof it.
Balancing usability and security, zkVerify’s multi-proof support lets projects mix systems: Groth16 for speed, Plonk for universality. In practice, hackathon winners like ZeroKnowledgeVoting showcase decentralized systems leveraging these for tamper-proof polls. As adoption grows, expect zkVerify to underpin not just elections, but DAOs and shareholder votes, where privacy drives participation.
Projects like kuronosec’s zk-voto-digital on GitHub illustrate this potential, protecting national identities with ZK proofs while zkVerify handles the heavy lifting of verification. This synergy scales privacy without compromising speed, positioning zkVerify protocol as the backbone for next-generation governance.
Hands-On Integration: Building with zkVerify
Developers eyeing zero knowledge proofs elections start by grasping zkVerify’s API endpoints for proof submission and verification queries. Its SDKs, tailored for Rust and Solidity, streamline cross-chain interactions. Benchmarks from the mainnet launch confirm sub-millisecond verifications for Groth16 proofs, with throughput hitting thousands per second, far outpacing Ethereum’s constraints. This efficiency empowers VeraVote privacy zk apps to process voter proofs in batches, minimizing latency during peak election hours.
Usability hinges on intuitive tooling. zkVerify’s dashboard offers real-time metrics on proof queues and success rates, aiding debugging. For election builders, this means simulating millions of votes pre-launch, ironing out bottlenecks early. Yet balance demands caution: while costs plummet 90%, network congestion during high-stakes polls could still spike fees, underscoring the need for hybrid on-off chain strategies.
Code in Action: Verifying Voter Proofs
Let’s examine a practical snippet for a Solidity contract interfacing with zkVerify. This example assumes a voter proof attesting eligibility and choice, verified via zkVerify’s UltraPlonk verifier. The contract emits events for transparent tallies, blending privacy with auditability.
PrivacyVoting Contract: Submitting ZK Proofs and Tallying Votes
This Solidity contract integrates with a zkVerify verifier to process privacy-preserving votes. A zero-knowledge proof is submitted, verifying the voter\u2019s eligibility and vote choice (0 for option A, 1 for option B) via public signals, including a nullifier hash to prevent double-voting. On success, tallies are updated.
```solidity
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.0;
interface IzkVerifyVerifier {
function verifyProof(
uint[2] calldata _pA,
uint[2][2] calldata _pB,
uint[2] calldata _pC,
uint[2][2] calldata _pubSignals
) external view returns (bool);
}
contract PrivacyVoting {
IzkVerifyVerifier public immutable verifier;
mapping(bytes32 => bool) public nullifierHashes;
uint256 public voteTallyA;
uint256 public voteTallyB;
event VoteCast(bytes32 indexed nullifierHash, uint8 vote);
constructor(address _verifier) {
verifier = IzkVerifyVerifier(_verifier);
}
function submitVote(
uint[2] calldata _pA,
uint[2][2] calldata _pB,
uint[2] calldata _pC,
uint[2][2] calldata _pubSignals,
bytes32 _nullifierHash
) external {
require(!nullifierHashes[_nullifierHash], "Vote already cast");
// Assume pubSignals[0][0] is nullifierHash (scaled), pubSignals[0][1] is vote (0 or 1)
uint256 pubNullifier = uint256(_pubSignals[0][0]);
uint8 vote = uint8(_pubSignals[0][1]);
require(bytes32(pubNullifier) == _nullifierHash, "Nullifier mismatch");
require(vote == 0 || vote == 1, "Invalid vote value");
nullifierHashes[_nullifierHash] = true;
bool isValid = verifier.verifyProof(_pA, _pB, _pC, _pubSignals);
require(isValid, "ZK proof verification failed");
if (vote == 0) {
voteTallyA += 1;
} else {
voteTallyB += 1;
}
emit VoteCast(_nullifierHash, vote);
}
function getResults() external view returns (uint256 a, uint256 b) {
return (voteTallyA, voteTallyB);
}
}
```Key features include on-chain proof verification for trustlessness, nullifier-based anti-double-spending, and public vote tallies. Deploy by providing the zkVerify verifier contract address. Public signals must match the proof circuit exactly; adjust based on specific zkVerify configuration and proof system (e.g., Groth16).
Such implementations reveal zkVerify’s edge: modular verifiers adapt to evolving circuits without hard forks. In VeraVote’s stack, this verifies proofs linked to anonymized IDs, ensuring one-person-one-vote without traceability. Hackathon entries like ZeroKnowledgeVoting extend this to fully decentralized setups, where smart contracts enforce rules end-to-end.
Real-world traction builds steadily. As of March 2026, zkVerify’s mainnet processes proofs for diverse apps beyond voting, from DeFi privacy to supply chain audits. VeraVote’s X posts signal growing partnerships, with community feedback emphasizing production-grade reliability. Independent voices, like Kennix’s commentary, affirm the shift from theoretical promise to deployable integrity.
Future Horizons: Scaling Privacy at Stake
Looking ahead, ZKV Protocol zk proofs could redefine global elections. Imagine nation-state pilots where zkVerify aggregates proofs across borders, enabling verifiable tallies for international referendums. Its support for RiscZero and SP1 opens doors to confidential computation on user devices, slashing centralization risks. Data from early adopters projects 100x scalability gains, sufficient for planetary-scale participation.
Challenges persist, demanding nuance. Voter education on proof generation remains key; not every smartphone matches optimized circuits. Regulatory hurdles, like data sovereignty, test blockchain’s borderless ethos. Still, zkVerify’s agnostic approach, embracing multiple systems, fosters resilience. Projects like VeraVote prove the model: privacy isn’t zero-sum with verifiability. As ZK proof verification network matures, it equips democracies with tools to withstand digital threats, fostering trust through code, not custodians.
Election integrity evolves from fragile paper to cryptographic certainty, with zkVerify accelerating the transition. Developers and advocates alike stand to gain from its open infrastructure, paving verifiable paths forward.