FHE ZK-SNARKs Integration Guide for Private DeFi Smart Contracts

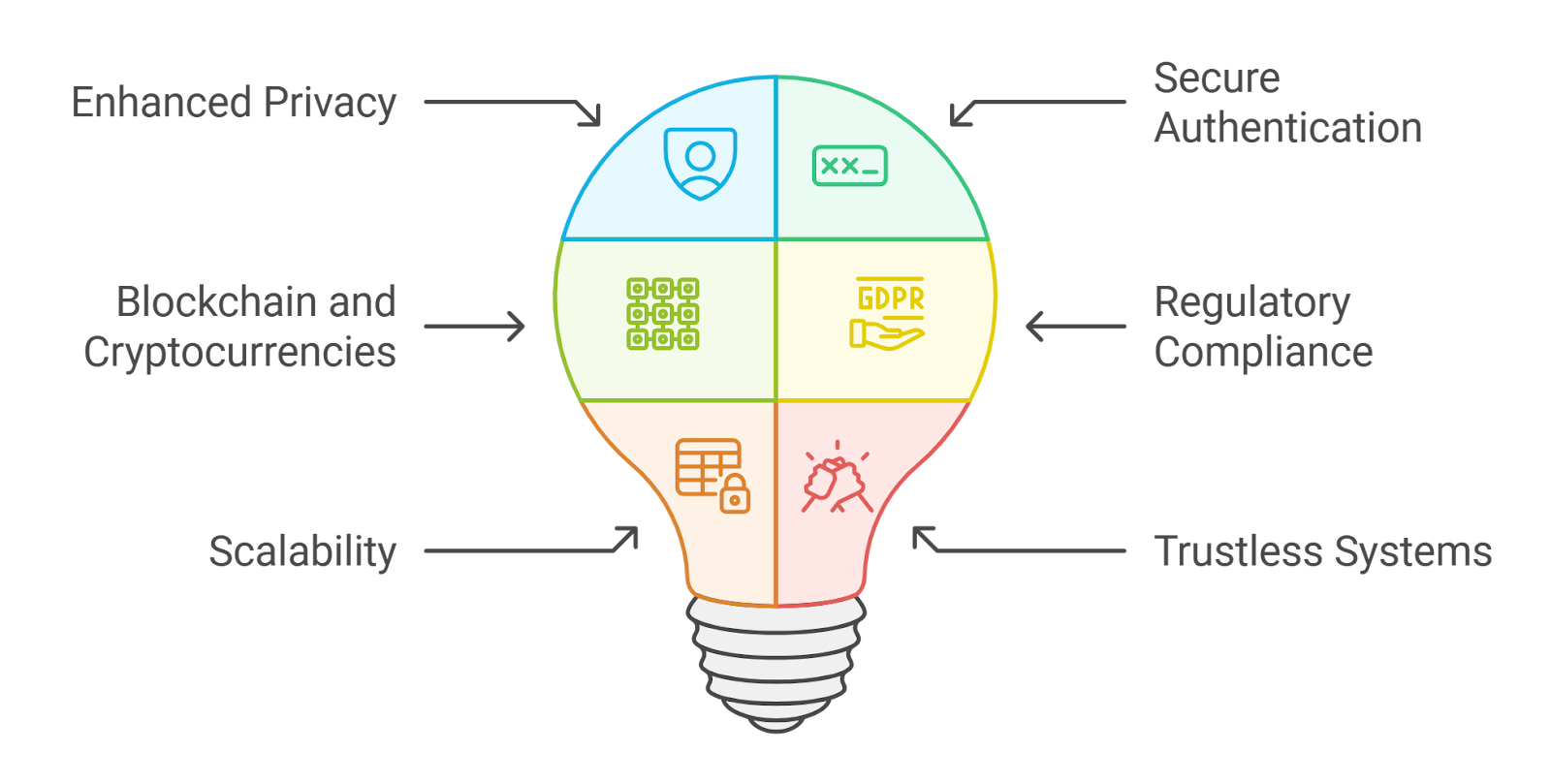
In the high-stakes world of decentralized finance, where every transaction lays bare user balances and strategies, true privacy remains elusive. Enter the potent duo of Fully Homomorphic Encryption (FHE) and ZK-SNARKs: a fusion that promises confidential DeFi computations without sacrificing verifiability. FHE lets smart contracts crunch numbers on encrypted data, while ZK-SNARKs prove the math checked out, all without peeking inside. This FHE ZK-SNARKs integration isn’t just theoretical; it’s the backbone for private DeFi smart contracts that can rival centralized vaults in secrecy.
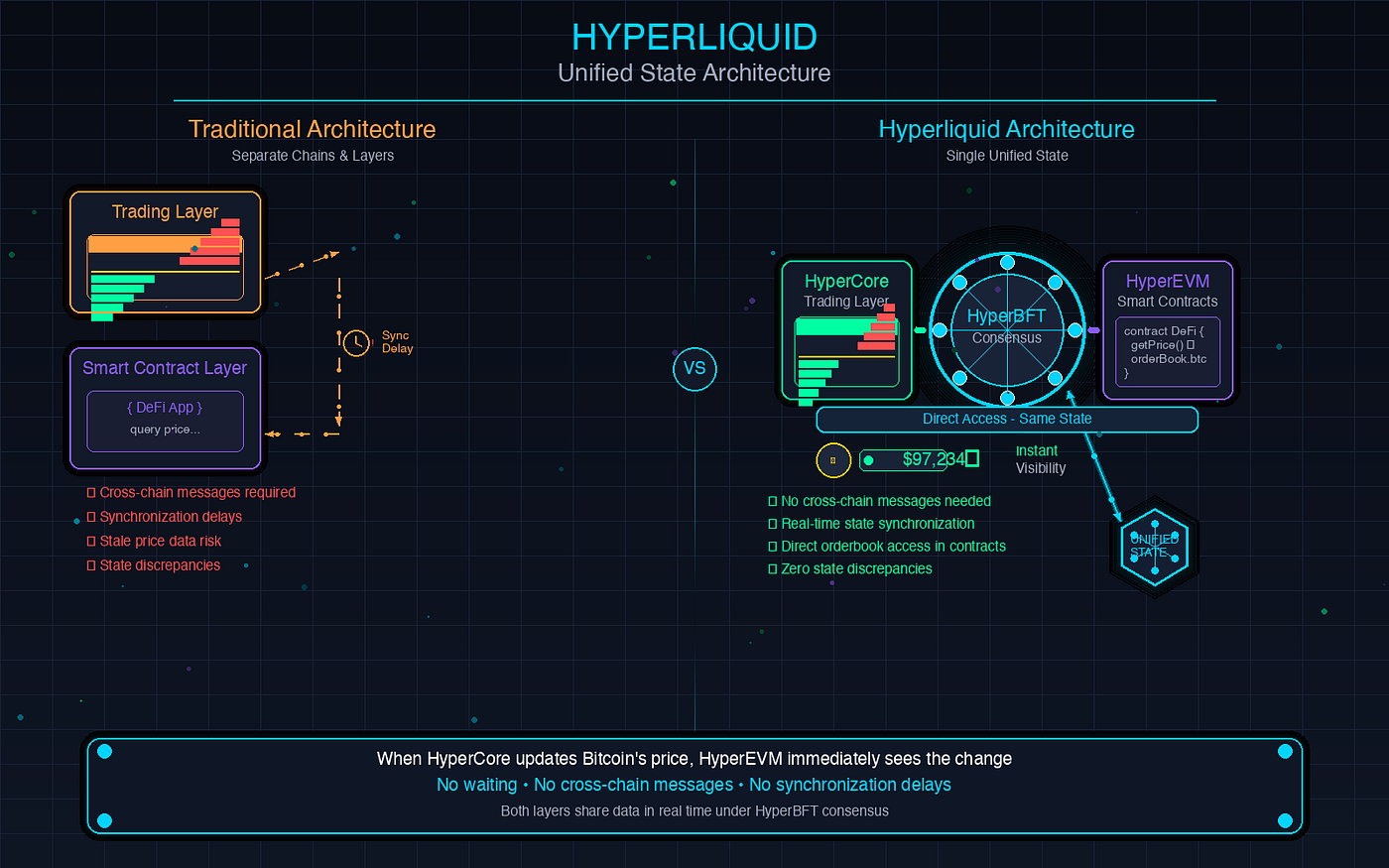
DeFi protocols today leak too much. Public ledgers expose trade sizes, wallet histories, even liquidation risks. Regulators hover, front-runners lurk, and users demand better. Zama’s push for chain-agnostic confidential contracts highlights this shift, blending FHE’s computation-on-ciphertext with zk-proofs for any EVM-compatible blockchain. Yet, as papers from Frontiers and arXiv note, dynamic rules and recursive proofs demand more than off-the-shelf ZK; they need FHE’s heavy lifting for real-world homomorphic encryption zk proofs.
Core Mechanics: How FHE Powers ZK-Enhanced Privacy
FHE flips the script on encryption. Traditional schemes decrypt before compute; FHE operates directly on ciphertexts, outputting encrypted results. Think lending pools evaluating collateral values without revealing borrower details. Libraries like those in Zama’s stack or open-source TFHE variants make this feasible, though gas costs loom large.
ZK-SNARKs enter as the verifier’s best friend. They compress complex computations into tiny proofs, verifiable in milliseconds. Alone, ZK struggles with stateful ops or heavy arithmetic; pair it with FHE, and you get encrypted inputs proven correct via succinct arguments. Recent benchmarks from USENIX and GitHub’s ZK-Bench reveal the gap: research-grade SNARKs prove fast, but on-chain deployment lags without FHE offloading encryption noise.
FHE ZK-SNARKs Benefits for Private DeFi
-
Encrypted lending without exposure: FHE enables interest calculations on encrypted borrower balances and rates, keeping data confidential per Zama’s blockchain integration.
-

Verifiable yields on hidden positions: ZK-SNARKs prove correct yield computations without revealing underlying asset positions or strategies.
-

Compliant privacy via shielded proofs: ZK-SNARKs generate succinct proofs for regulatory audits, as in Shielded CSV on Arbitrum for DeFi privacy-compliance.
-
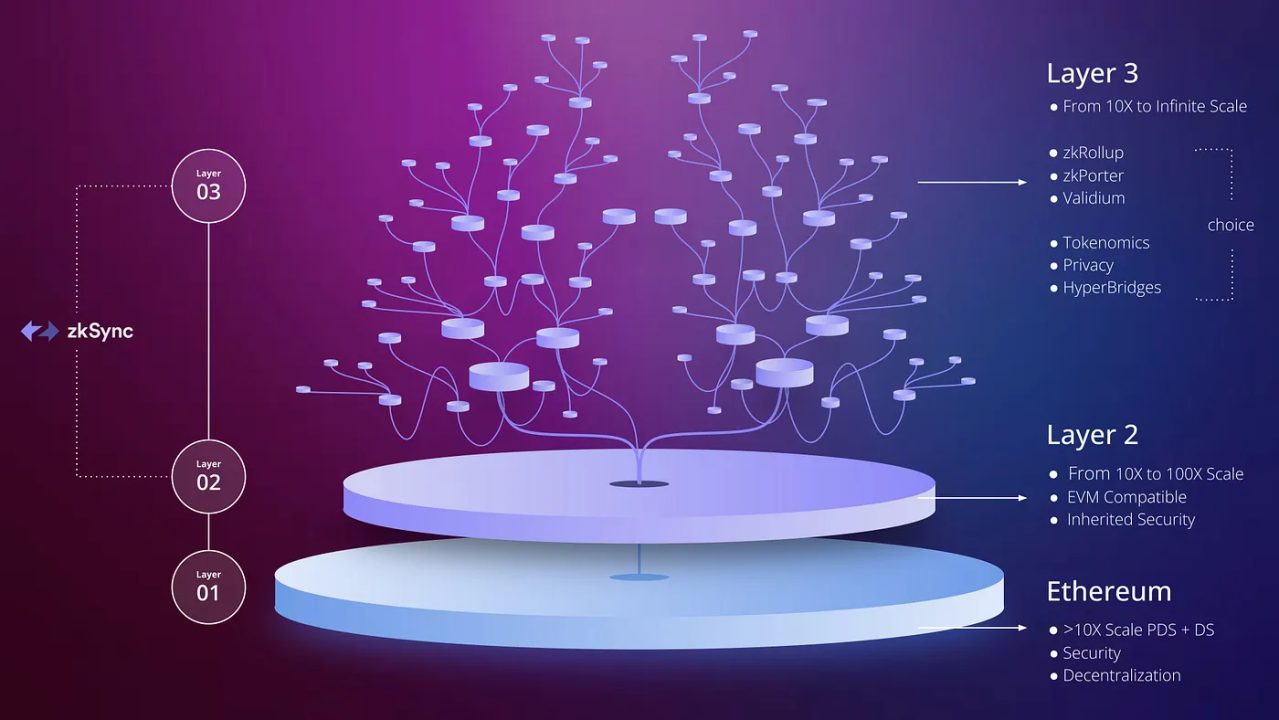
Scalable across L1/L2 chains: Zama FHE integrates with any smart contract-enabled blockchain, supporting L1 like Ethereum and L2 like Arbitrum.
-
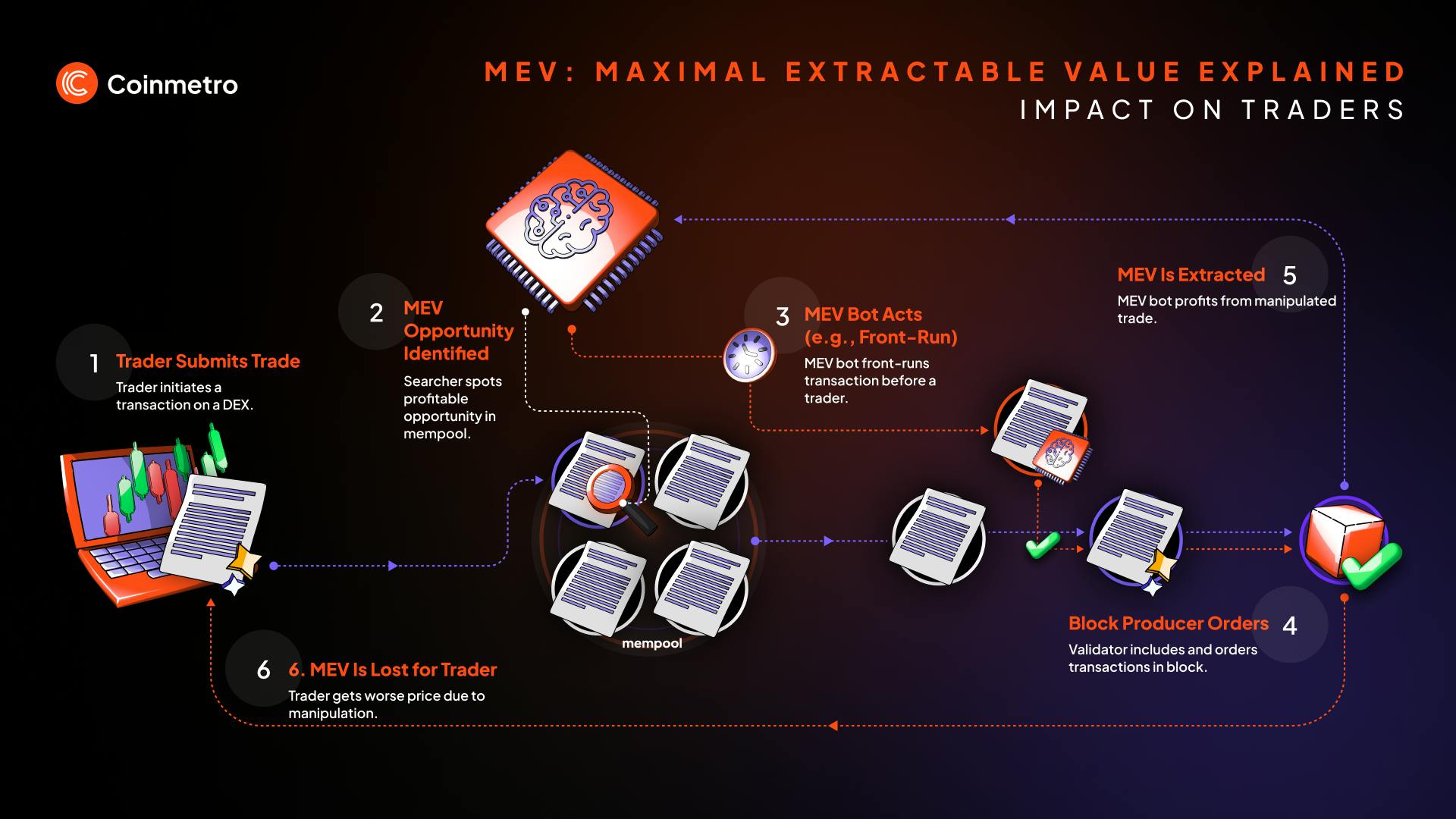
Reduced MEV from obscured orders: Encrypted orders hide details from mempools, preventing front-running in DeFi trades.
This synergy shines in use cases like shielded CSV on Arbitrum, as Genesis Hukou analyzes. Balances stay private, yet auditors verify compliance through ZK. It’s balanced progress: innovation tempers risk, echoing my FRM roots in crypto.
Navigating Integration Hurdles in DeFi Environments
Don’t romanticize it; FHE for blockchain privacy packs challenges. Circuit bloat from homomorphic ops can balloon proof sizes 10x. Proving time? Hours for non-trivial contracts. Tools like zk-Harness help benchmark, but developers need streamlined flows.
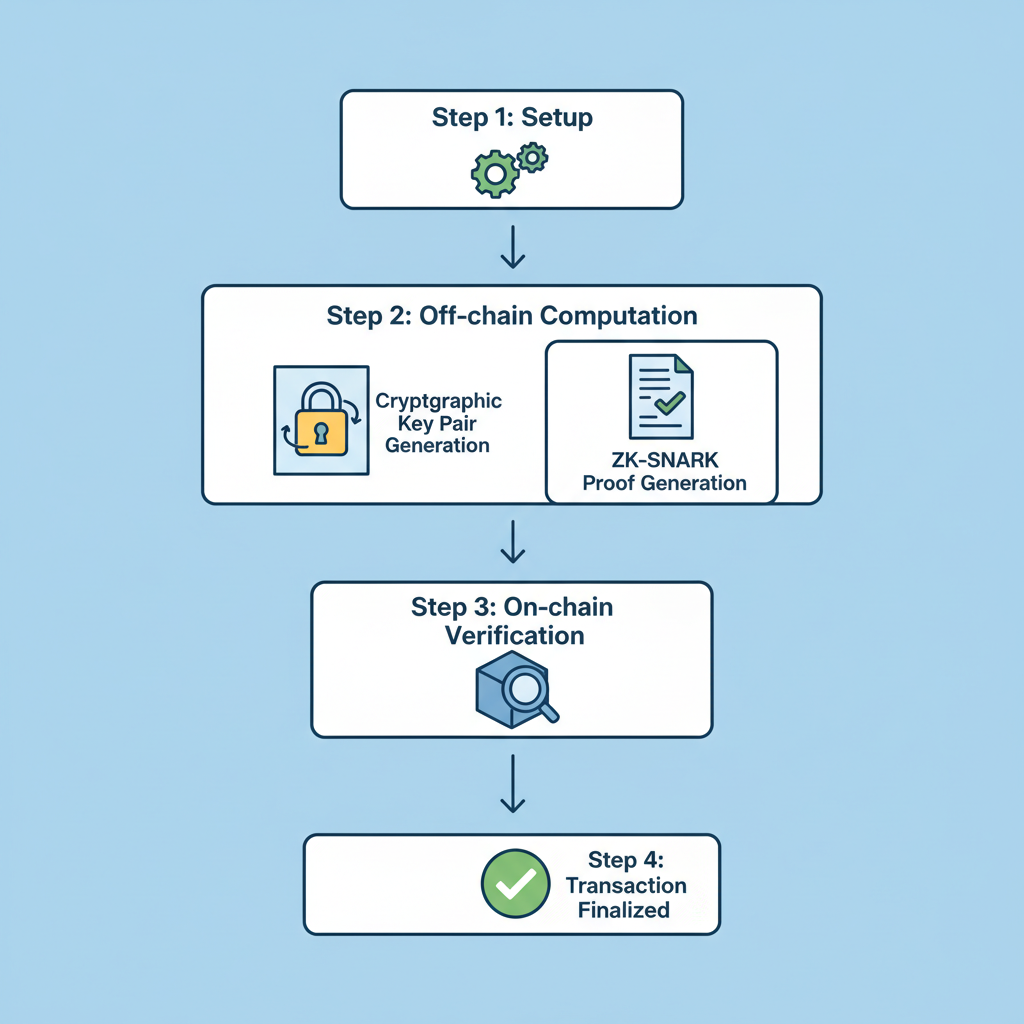
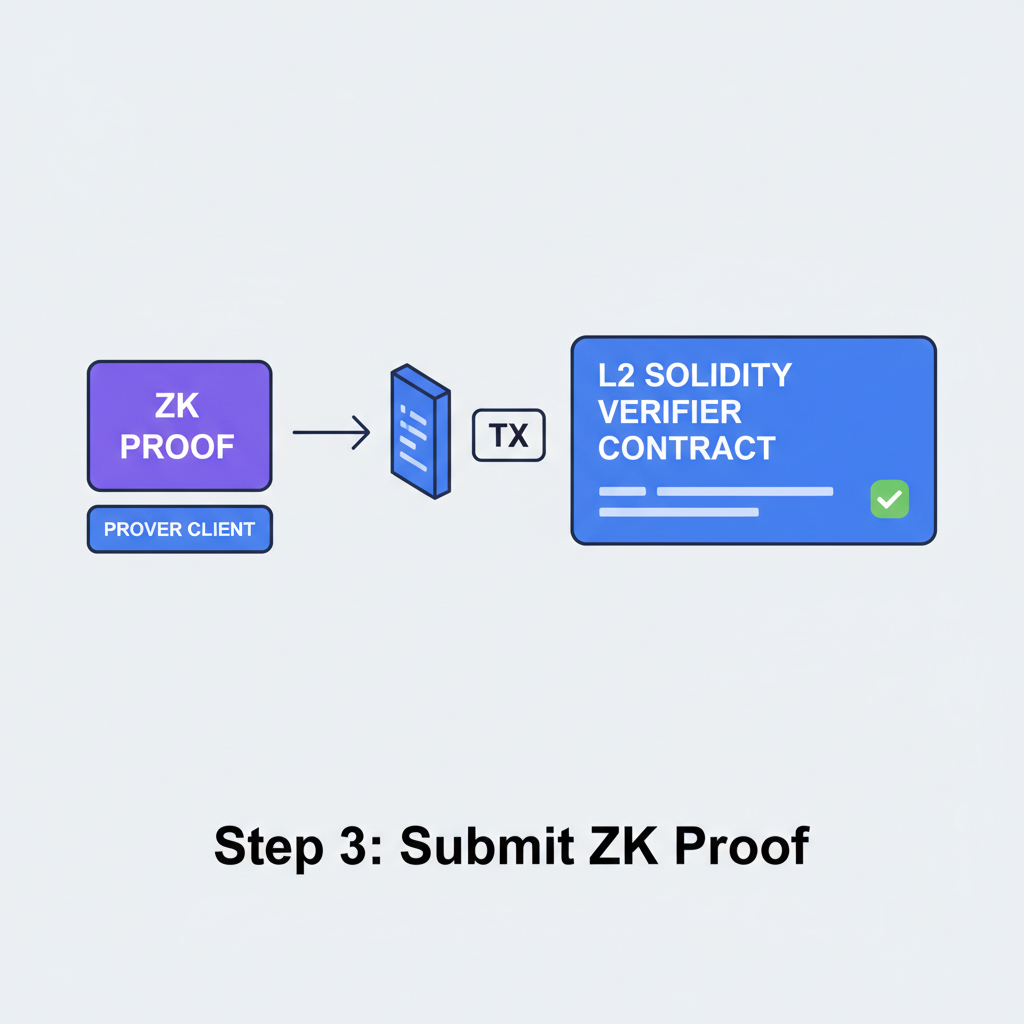
Start with hybrid architectures. Off-chain FHE compute generates encrypted intermediates; on-chain ZK verifies. TU Wien’s DKG via SNARKs shows dispute resolution without keys exposure. For DeFi, wrap FHE in Circom or Noir circuits: encrypt inputs client-side, submit to contract, prove execution. Rapid Innovation’s guide nails scaling tips, emphasizing recursive SNARKs for state proofs.
Risk management is key. Noise growth in FHE limits depth; bootstrap wisely or cap operations. Quantum threats? STARKs loom, but SNARKs suffice for now with trusted setups managed. Opinion: prioritize L2s like Arbitrum for cheaper proofs, avoiding L1 gas traps.
Developer Roadmap: First Steps to Deployment
Hands-on begins with tooling. Clone Zama’s repo or tfhe-rs for Rust-based FHE. Craft a simple circuit: say, private swap proving equal value post-fee without revealing amounts. Use snarkjs for Groth16 proofs, integrating FHE-packed inputs.
Circom Circuit: Verifying FHE-Encrypted Swap Inputs
This Circom circuit provides a practical example for verifying FHE-encrypted inputs in a DeFi swap. It ensures the private swap amount falls within predefined minimum and maximum bounds without revealing the value, enabling privacy-preserving validation.
```circom
pragma circom 2.0.0;
template FHESwapInputVerifier {
signal input swapAmount;
signal input maxSwap;
signal input minSwap;
signal output isValid;
// Check swapAmount > minSwap and swapAmount <= maxSwap
// Using simplified comparison (in practice, use circomlib comparators for bit-length safety)
component greaterThanMin = GreaterThan(128);
greaterThanMin.in[0] <== swapAmount;
greaterThanMin.in[1] <== minSwap;
component lessEqMax = LessEqThan(128);
lessEqMax.in[0] <== swapAmount;
lessEqMax.in[1] <== maxSwap;
isValid <== greaterThanMin.out * lessEqMax.out;
// Enforce validity constraint
isValid * (1 + minSwap - swapAmount) === isValid;
isValid * (swapAmount - maxSwap) === 0;
}
component main {publicSignals: [isValid]} = FHESwapInputVerifier();
```
Note: This uses components from circomlib/circuits/comparators.circom (import required in full code). Compile with `circom circuit.circom --r1cs --wasm --sym` to generate proofs for smart contract integration. Adjust bit widths for your security parameters.
Test locally with Hardhat, then deploy. Benchmarks matter: zk-authfeed protects oracles similarly. Balance compute: FHE for privacy, ZK for trustlessness. This half sets the stage; next, deep dives into optimizations await.
Optimizations start with scheme selection. TFHE's leveled FHE minimizes bootstrapping overhead for DeFi's fixed-depth ops like yield calcs. Pair with PLONK or Groth16 SNARKs via arkworks for faster proving; GitHub's ZK-Bench confirms 30% gains. Offload FHE to sequencers in rollups, verifying aggregates on-chain. This homomorphic encryption zk proofs stack slashes latency from days to minutes, viable for production private lending.
Real-World Builds: From Testnets to Mainnet DeFi
Shielded CSV on Arbitrum exemplifies success. Users submit encrypted CSVs; FHE computes totals privately, ZK-SNARKs attest compliance sans data leak. Genesis Hukuk's analysis flags regulatory wins: privacy meets KYC via selective disclosure. Zama's chain-agnostic FHE extends this to Ethereum, Polygon, even Cosmos, per Nina Drokina's Medium deep-dive. Hyper-heuristic papers from Frontiers hint at adaptive rules, where FHE handles dynamic rates under ZK scrutiny.
ScienceDirect's real estate contracts mirror DeFi swaps: zk-SNARKs shield bids, FHE values properties encrypted. TU Wien's DKG integrates keys for threshold sigs in vaults, disputing via SNARKs. Hacken's breakdown stresses trusted setup hygiene; rotate ceremonies or pivot to STARKs for post-quantum. My take: start small, like oracle feeds via zk-authfeed, scaling to full AMMs.
Performance tuning demands nuance. USENIX benchmarks expose on-chain verifier bloat; use precompiles or custom opcodes where chains allow. Rapid Innovation's 2024 guide pushes recursive composition: inner FHE proofs aggregated into outer SNARKs, compressing state for L1 settlement. Opinionated advice: benchmark relentlessly with zk-Harness. L2s like Optimism cut costs 90%, but watch sequencer centralization risks.
Solidity Verifier for FHE-ZK Proofs in Private Lending Pool
In a private DeFi lending pool using FHE-ZK-SNARKs, the verifier contract checks proofs that computations on encrypted user data (e.g., collateral sufficiency) were performed correctly without revealing sensitive details. Here's a practical Solidity snippet integrating a Groth16 verifier:
```solidity
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.19;
import "./Groth16Verifier.sol"; // Assume pre-generated Groth16 verifier library
contract PrivateLendingPoolVerifier {
Groth16Verifier public immutable verifier;
constructor(address _verifier) {
verifier = Groth16Verifier(_verifier);
}
struct FHEZKProof {
uint[2] a;
uint[2][2] b;
uint[2] c;
}
struct PublicSignals {
uint[1] collateralRatio; // e.g., hashed or public value for verification
}
/// @notice Verifies FHE-ZK proof for private lending conditions
/// @dev Confirms borrower collateral >= loan amount without revealing privates
function verifyFHEZKProof(
FHEZKProof calldata proof,
PublicSignals calldata pubSignals
) external view returns (bool) {
uint[2] memory pA = proof.a;
uint[2][2] memory pB = proof.b;
uint[2] memory pC = proof.c;
uint[1] memory input = pubSignals.collateralRatio;
return verifier.verifyProof(pA, pB, pC, input);
}
}
```Deploy this with a circuit-specific Groth16 verifier (generated via circom/snarkjs). Public signals might include a commitment to the loan terms. Always audit pairings and test on testnets for gas efficiency and security.
Mainnet pilots emerge. Mir Protocol's Zk-Layer1 layers FHE atop SNARKs for cross-chain privacy. DeFi's privacy-regulation bind dissolves: shielded proofs enable audits without exposure. Yet balance reigns; over-reliance on FHE invites side-channel leaks if bootstraps falter. Mitigate with multi-scheme hybrids, testing via ZK-Bench suites.
Scaling Private DeFi: Tools and Best Practices
Tooling matures fast. Noir's high-level circuits abstract FHE noise; integrate with Foundry for E2E tests. For confidential AMMs, encrypt order books client-side, FHE-match off-chain, ZK-post on-chain. Gas? Profile with recursive SNARKs from arXiv's sidechain work. Checklist: secure keygen, cap circuit depth at 20 levels, validate proofs pre-submit.
Enterprise angles intrigue. FHE for blockchain privacy suits tokenized assets, where collateral stays hidden yet verifiable. Frontiers' hyper-heuristics automate risk models on encrypted positions, ZK-proven. Challenges persist: developer ramp-up, as USENIX gaps show. Bridge with tutorials, like Rapid Innovation's ZKP playbook tailored to smart contracts.
This integration redefines private DeFi smart contracts. From encrypted yields to shielded liquidations, FHE ZK-SNARKs deliver confidential DeFi computations that withstand scrutiny. Progress accelerates, but measured steps ensure resilience. Developers, prototype today; the vaults of tomorrow demand it.