Formal Verification of zkVMs: Ensuring Correctness in RISC Zero Knowledge Machines

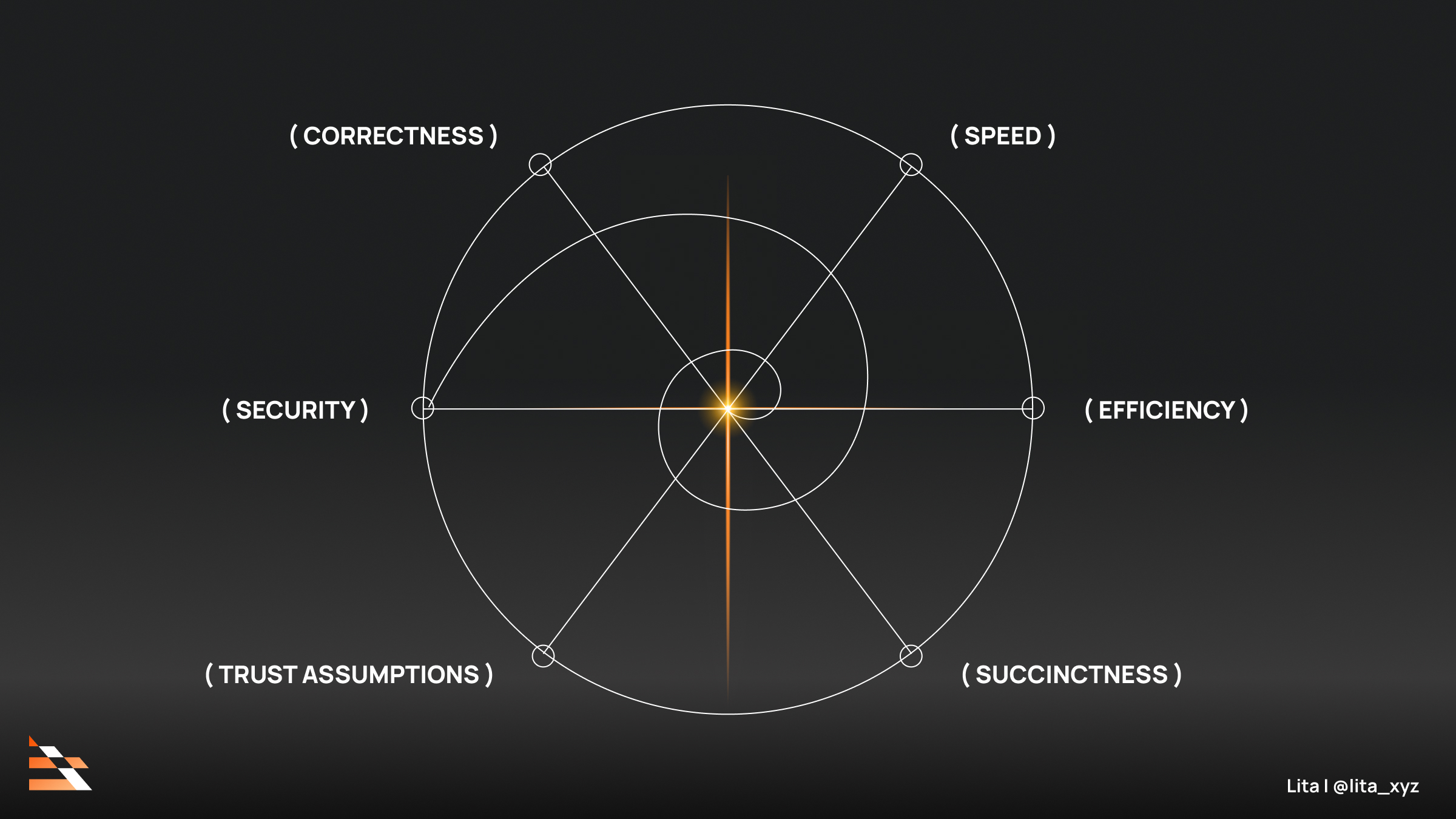
Zero-Knowledge Virtual Machines (zkVMs) power the next wave of verifiable computation in blockchain ecosystems, allowing complex off-chain logic to be proven on-chain without exposing inputs. RISC Zero’s zkVM, built on the RISC-V architecture, exemplifies this potential through its general-purpose execution environment. However, the intricate layers of circuit generation, intermediate representations, and proof systems harbor subtle bugs that threaten ZK proof correctness. Formal verification emerges as an indispensable discipline to certify these systems, bridging theoretical soundness with practical reliability.

Few domains demand such rigorous scrutiny as zkVM formal verification. Traditional testing falls short against the combinatorial explosion of states in zero-knowledge circuits. A single misstep in opcode semantics or memory modeling can invalidate proofs, eroding trust in rollups and DeFi protocols reliant on them. Recent incidents underscore this vulnerability: the Arguzz tool, blending metamorphic testing with fault injection, uncovered eleven bugs across six zkVMs, including a critical flaw in RISC Zero that earned a $50,000 bounty. Such findings compel a shift toward mathematically grounded assurances.
RISC Zero zkVM Verification Milestones
-

Nethermind’s Lean POC for Zirgen eDSL: GitHub repo risczero-fv models RISC Zero’s Zirgen eDSL and verifies POC zk circuits.
-

Core RISC-V instruction verification: Nethermind verifies key components of RISC Zero zkVM using Lean proof assistant.
-
SP1 Hypercube core verification: Collaboration with Succinct Labs formally verifies entire 64-bit RISC-V zkVM core in Lean.
-
Integration with Arguzz: Automated testing pipeline from ‘Arguzz’ paper detects soundness bugs in zkVMs like RISC Zero.
-
Veridise collaboration: RISC Zero partners with Veridise for first formally verified RISC-V zkVM.
Nethermind’s Lean Proof-of-Concept for RISC Zero zkVM
Nethermind’s Formal Verification team has charted a pragmatic path forward with a proof-of-concept targeting RISC Zero’s Zirgen embedded domain-specific language and its MLIR backend. Employing the Lean proof assistant, they model core components like register operations and control flow, establishing equivalence between high-level specifications and generated circuits. This approach yields high-assurance guarantees on the VM’s foundational logic, sidestepping the opacity of hand-optimized provers.
Their GitHub repository, NethermindEth/risczero-fv, hosts executable proofs for sample circuits, demonstrating feasibility at scale. By focusing on MLIR as the verification pivot, Nethermind isolates verification from prover-specific details, enhancing reusability across STARK or SNARK backends. Conservatively, this methodology halves the trusted code base, a material reduction in attack surface for RISC Zero zkVM deployments.
Lean as the Assistant of Choice in ZK Verification
Lean’s dependent type theory proves uniquely suited to zkVMs, enforcing invariants that static analysis overlooks. Succinct Labs leveraged it to verify the entire 64-bit core of their SP1 Hypercube RISC-V zkVM, confirming alignment with RISC-V semantics down to cycle-accurate execution. Nethermind extended this to RISC Zero in partnership, modeling Zirgen’s eDSL constructs and proving preservation of program traces through compilation stages.
This conservative choice prioritizes mechanized proofs over pen-and-paper arguments, which have faltered in cryptographic history. Galois complements these efforts by proving Jolt zkVM’s frontend against Sail-defined RISC-V semantics in Lean 4, targeting Ethereum’s verification needs. Collectively, these initiatives signal a maturing toolchain for Nethermind ZK research, where reproducibility trumps novelty.
RISC Zero’s Proactive Verification Roadmap
RISC Zero advances on multiple fronts, partnering with Veridise to integrate the Picus framework for automated, continuous verification of their RISC-V zkVM. This targets elimination of soundness bugs through differential execution checks against golden RISC-V models. Meanwhile, their Zisk environment explores Nethermind client binaries, fusing execution fidelity with zero-knowledge efficiency.
Opinionated view: while zkVMs like NockVM pursue minimal ISAs for circuit efficiency, RISC Zero’s full-featured RISC-V stance demands exhaustive formal methods to sustain generality without sacrificing security. Arguzz’s real-world bug hunts validate this rigor; undetected flaws could cascade into multi-million-dollar exploits in production rollups.
Undetected vulnerabilities in zkVMs extend beyond isolated incidents, posing systemic risks to the scalability of ZK-rollups. RISC Zero’s commitment to formal methods, evidenced by its Veridise partnership and Picus integration, positions it as a leader in mitigating these threats through automated, reference-model comparisons. This conservative strategy prioritizes incremental progress over ambitious overhauls, fostering deployable confidence in RISC Zero zkVM for enterprise-grade applications.
Arguzz: Rigorous Testing Sharpens Verification Edges
Automated tools like Arguzz augment formal verification by exposing edge-case flaws that manual proofs might overlook. This metamorphic testing framework injects faults into zkVM inputs, comparing outputs against expected behaviors across RISC Zero, Nexus, Jolt, SP1, OpenVM, and Pico. Its detection of eleven bugs, including a high-value RISC Zero vulnerability, highlights the interplay between empirical testing and mathematical proofs in achieving ZK proof correctness.
Conservatively assessed, Arguzz’s methodology reveals that even mature zkVMs harbor completeness gaps, where valid computations fail to prove. Integrating such tools into CI/CD pipelines complements Lean’s static guarantees, creating layered defenses essential for production environments. Nethermind’s ZK audits, blending these techniques, exemplify full-stack coverage that Nethermind ZK research delivers to protocols under scrutiny.
Community-Wide Initiatives Toward Verified Verifiers
The ZKProof ‘Verified Verifiers’ working group addresses a critical upstream concern: validator software integrity. By formalizing verification steps for diverse ZKP schemes, it establishes replicable standards that downstream zkVMs like RISC Zero can leverage. This bottom-up rigor counters the verifier’s paradox, where proof soundness hinges on unverified code.
Galois’s work on Jolt zkVM, mechanically aligning frontend semantics with Sail-modeled RISC-V in Lean 4, extends this ethos to Ethereum-centric verification. Meanwhile, NockVM’s minimalistic design formalizes a lean ISA as an efficient circuit, trading breadth for provable performance. These orthogonal paths underscore a diversified landscape where zkVM formal verification evolves from siloed efforts to ecosystem standards.
Investment Implications for Privacy Technologies
From a fundamental analysis perspective, formally verified zkVMs like RISC Zero’s enhance long-term protocol viability, underpinning DeFi and rollup valuations. Reduced bug bounties and exploit risks translate to lower insurance premiums and higher TVL, driving sustainable market value. Projects ignoring verification face discounting akin to unproven bridges, as investors demand audited primitives.
Nethermind’s toolchain, Succinct’s Hypercube proofs, and Arguzz’s validations signal maturation. Yet, challenges persist: scaling proofs to full ISA coverage without proof-size explosions requires ongoing innovation. RISC Zero’s roadmap, fusing Picus automation with Lean models, offers a blueprint for balancing generality and assurance.
Stakeholders in Web3 should monitor these developments closely. Verified zkVMs not only fortify computational privacy but also unlock enterprise adoption, where regulatory scrutiny amplifies the premium on correctness. In an arena defined by trust-minimized execution, formal verification stands as the bedrock of enduring value.












